Penetration Testing Grows Due to Remote Work
Cybersecurity professionals are requested to conduct more penetration testing and security assessments focusing on remote work during the COVID-19 pandemic than ever before.
With the rapid transition to work from home during the COVID-19 pandemic, the organizations’ attack surface has evolved, and security measures could not remain unchanged. Businesses that care about their cybersecurity have shifted priorities to protect their network infrastructure, focusing on the growing risks of remote work, with pentesting as the means of immediate improvement.
Based on the 2021 Core Security Penetration Testing Survey report, we highlight the recent trends in the pentesting industry. This report summarizes the results of a comprehensive survey of cybersecurity professionals around the globe. The goal was to present an accurate analysis of how organizations benefit from penetration testing in these trying times.
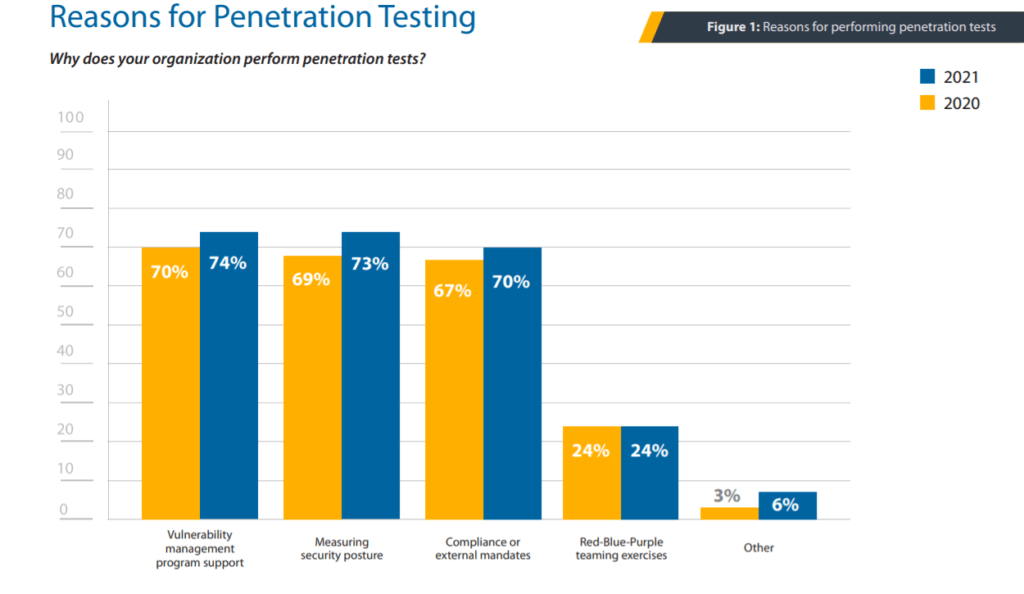
Reasons for penetration testing
Organizations undergo pentests for three primary reasons: measuring their security posture, supporting the vulnerability management program, and meeting compliance requirements.
Pentesting challenges and opportunities for third-party pentesting providers
Organizations indicate hiring skilled personnel to do the internal penetration tests as the most significant pentesting challenge. Moreover, during 2021, companies consumed twice as much third-party pentesting services as in 2020 to achieve their security testing objectives. It means the demand for outsourcing penetration testing and application security services increases, and the cybersecurity market shows steady growth, despite the obstacles.
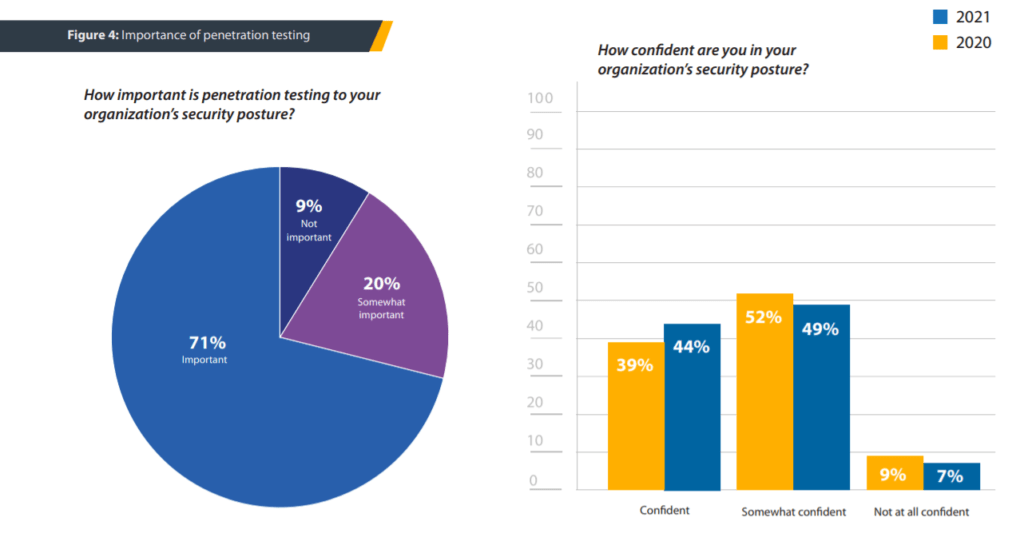
Penetration testing is essential to your organization’s security
71% of organizations have reported that pentesting is essential for their security program, and 20% said it is somewhat important. Only 9% of respondents do not emphasize on pentesting importance to their companies.
According to another source, the “CEO Survey” published by PwC, the security threats are second to only the pandemic and health crisis when assessing the risks to the organization’s growth prospects.
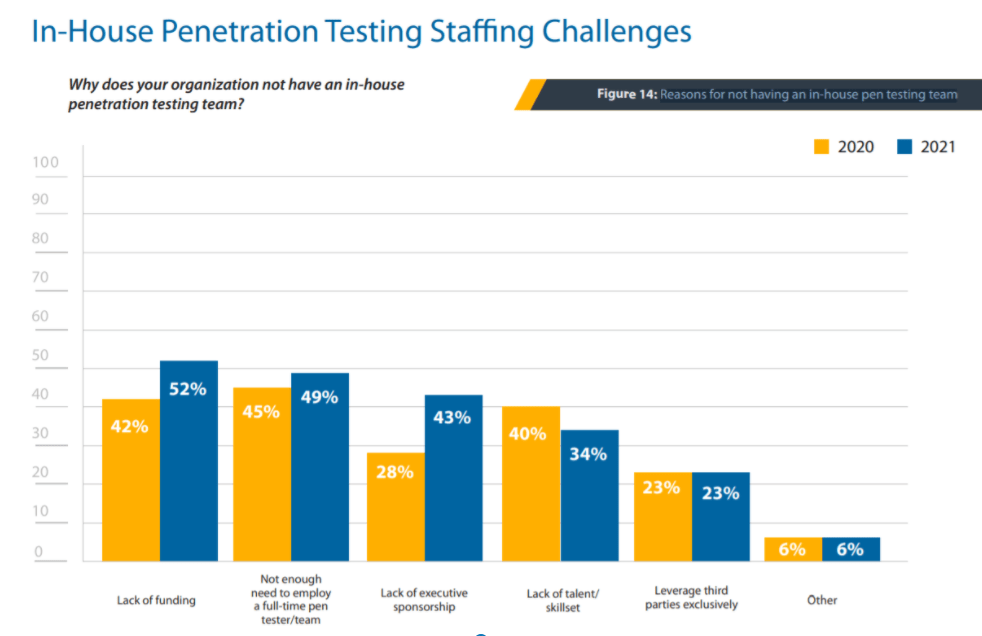
In-house penetration testing staffing challenges
Many reasons prevent organizations from having an in-house internal pentesting team. The majority of respondents (52%) named the lack of funding as the most challenging obstacle. 49% said their organizations do not have enough need to employ a full-time pentesting team. And 43% reported the lack of executive sponsorship as the primary blocker. All these figures have grown compared to the previous year’s survey results.
In 2021, fewer companies named the lack of skilled candidates as an obstacle, and a fraction of companies that prefer using third-party pentesting service providers remained unchanged.
Increased demand in Work from Home penetration testing
Because of the rise in the number of permanent network connections and extension of the related attack surface, network security tests increased in 45% of organizations. 38% of the companies broadened their penetration testing scope. 36% of respondents added more effort on web application security tests, as the use of corporate web apps surged. And 31% of organizations determined social engineering penetration testing of the remote workforce as a priority.
How often organizations conduct third-party pentests?
Third-party teams run penetration tests annually in 53% of organizations, 23% of organizations have pentests quarterly, and 12% do pentests every 2-3 years.
Why do organizations engage third-party penetration testers?
When they can, organizations use both in-house pentesting teams and third-party penetration testing service providers. Internal pentesting teams are great for ensuring continuous security assessment. IT environments are constantly changing, security bugs and configuration mistakes could easily open new attack vectors. This is when consistent and continuous internal pentesting pays off.
Third-party pentesting service providers are valued for their independent review and expert advice, and for bringing a fresh perspective on security to the organization. Respondents most frequently (63%) cited the external, objective mindset as a reason for using third-party pentesting teams. Organizations also order external penetration testing services to meet compliance requirements and apply professional services of pentesting full-time experts where internal teams may lack skills or experience.
Conclusion
This survey aimed to guide organizations and cybersecurity professionals on how to benefit from penetration testing in the new reality of the global pandemic. As observed, in-house pentesting operations and third-party professional services experience consistent growth. In-house pentesting teams remain widespread, while larger organizations strive to combine in-house and outsourcing approaches to pentesting. Small companies and startups look for trustworthy pentesting partners to provide regular infrastructure and product security assessments.
Remote work increases the attack surface, and Work from Home security assessments become a priority in regular penetration tests. Organizations protect their employees at times of global pandemic by allowing them to safely work from home, which increases social engineering risks that need proper assessment and treatment.
Internal and external penetration testing teams serve the organizations by measuring their cybersecurity programs’ effectiveness, identifying areas of improvement, and building confidence in their security posture.
References
- Coresecurity 2021 Penetration Testing Report
- PwC 24th Annual Global CEO Survey